Got Privs? Crack Those Hashes!
Joff Thyer // Black Hills Information Security loves performing both internal penetration tests, as well as command and control testing for our customers. Thanks to the efforts of many great […]

Joff Thyer // Black Hills Information Security loves performing both internal penetration tests, as well as command and control testing for our customers. Thanks to the efforts of many great […]

Carrie Roberts* // (Updated, 2/11/2019) Trying to figure out the password for a password protected MS Office document? This free solution might do the trick. It attempts to guess the password […]
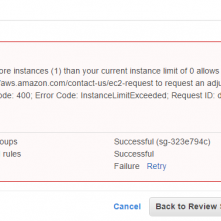
Carrie Roberts* // How does password cracking in the cloud compare to down here on earth? Maybe not as heavenly as imagined. I saw this on the web and got […]

Kent Ickler // The Task Buy The Things: Total for new password cracking machine$5110 A Few Quick Lessons The CPU cooler doesn’t actually clear the case cover. This was OK […]

Derek Banks // This post will walk through a technique to remotely run a Kerberoast attack over an established Meterpreter session to an Internet-based Ubuntu 16.04 C2 server and crack […]
Carrie Roberts // A tool to generate password usage statics in a Windows domain based on hashes dumped from a domain controller. The Domain Password Audit Tool (DPAT) is a […]
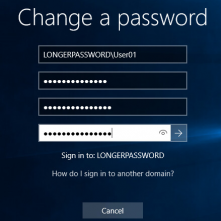
Kent Ickler // As a start to a series on Windows Administration in the eyes of a security-conscious “Windows Guy” I invite you on configuring AD DS PSOs (Password Security […]