Pink Teaming: The Dilution of Pentesting
John Strand // There have been a few conversations at conferences and meet-ups over the past year or so about the validity of penetration testing. There are many things on […]
John Strand // There have been a few conversations at conferences and meet-ups over the past year or so about the validity of penetration testing. There are many things on […]
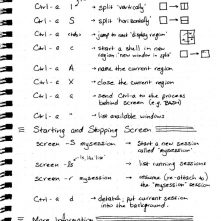
Brian King // I use GNU Screen mainly to prevent processes from dying when I disconnect from an SSH session, but GNU Screen can do a whole lot more than that […]

Derek Banks // As pentesters, it is probably not a surprise that we tend to make fairly heavy use of Kali Linux on a fairly regular basis. The folks at Offensive […]
Brian Fehrman // As described in my last blog post, Powershell Without Powershell – How To Bypass Application Whitelisting, Environment Restrictions & AV (sheeesh…it’s been a bit!), we are seeing more environments in […]
Joff Thyer // Editor’s Note: This is part 3 of a 3 part series. Part 1 discussed configuring your virtual machine engine and virtual hardware emulation. Part 2 covered installing Android […]
John Strand // So you think you might have a compromised Windows system. If you do, where do you start? How would you review the memory of that system? What […]

Joff Thyer // Editor’s Note: This is part 2 of a 3 part series. Part 1 discussed configuring your virtual machine engine and virtual hardware emulation. Part 2 (this part) covers […]

Joff Thyer // Editor’s Note: This is part 1 of a 3 part series. Part 1 will discuss configuring your virtual machine engine and virtual hardware emulation. Part 2 covers installing […]
John Strand with BHIS testers // Yes, we did this in 2017, but it’s reflecting work done in 2016.