Bugging Microsoft Files: Part 2 – Xlsx Files using Microsoft Excel
Ethan Robish // As promised in my previous post, part 1, this post shows how to place a tracking bug in a native .xlsx file. Full credit for this method […]
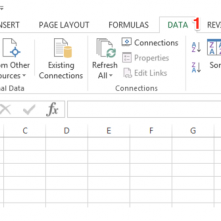
Ethan Robish // As promised in my previous post, part 1, this post shows how to place a tracking bug in a native .xlsx file. Full credit for this method […]
Carrie Roberts // There are various reasons why having a webDAV server comes in handy. The main reason I created one was to execute a malicious Outlook rule attack as […]

Ethan Robish // If you’re familiar with ADHD and Web Word Bugs, you likely already know the method to create web tracking software using .html files renamed as .doc files. […]

Beau Bullock // Full Disclosure: Black Hills Information Security believes in responsible disclosure of vulnerabilities. This vulnerability was reported to Microsoft on September 28th, 2016. As of the publication date of […]

David Fletcher & Sally Vandeven // We gave a presentation at the GrrCon hacker conference in Grand Rapids, MI on October 6, 2016. The presentation was a dialogue meant to illustrate the […]
David Fletcher // Reporting is a penetration testing topic that doesn’t have a whole lot of popularity. People have a hard time being inspired to write about the technical details of […]
David Fletcher // Weak NTFS permissions can allow a number of different attacks within a target environment. This can include: Access to sensitive information Modification of system binaries and configuration […]
Beau Bullock // I’ve added in a few modules to MailSniper that will assist in remote attacks against organizations that are hosting an externally facing Exchange server (OWA or EWS). Specifically, […]

Beau Bullock // TL;DR MailSniper is a penetration testing tool for searching through email in a Microsoft Exchange environment for specific terms (passwords, insider intel, network architecture information, etc.). It […]