What to Do with Your First Home Lab
Having assembled fundamental lab components, you now get to play! However, the ocean of potential projects can be intimidating. Where does one even start?

Having assembled fundamental lab components, you now get to play! However, the ocean of potential projects can be intimidating. Where does one even start?
This scenario simultaneously tests identity confirmation tooling (SSPR, MFA, Conditional Access), how users act under pressure, and the organization’s ability to detect and follow-up on social engineering attacks.

In today’s interconnected digital world, information security has become a critical concern for individuals, businesses, and governments alike. Cyber threats, which encompass a wide range of malicious activities targeting information systems, pose significant risks to the confidentiality, integrity, and availability of data.
Deceptive-Auditing is a tool that deploys Active Directory honeypots and automatically enables auditing for those honeypots.
This is the third in a three-part series of blog posts discussing how to abuse Kerberos delegation! If you haven’t already, feel free to read the first blog post, as they discuss the Kerberos authentication process and how delegation plays an important role in solving the double-hop problem, and how to abuse unconstrained delegation.
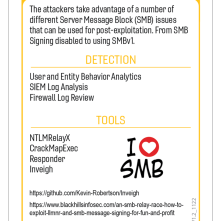
This article was written to provide readers with an overview of a selection of our pentest results from the last 15 months. This data was gathered toward the end of September 2025. Shockingly, the data does not differ much from our prior analyses conducted at the end of 2022 or 2023.

This is the second in a three-part series of blog posts discussing how to abuse Kerberos delegation! If you haven’t already, feel free to read the first blog post, as it discusses the Kerberos authentication process and how delegation plays an important role in solving the double-hop problem.

In Active Directory exploitation, Kerberos delegation is easily among my top favorite vectors of abuse, and in the years I’ve been learning Kerberos exploitation, I’ve noticed that Impacket doesn’t get nearly as much coverage as tools like Rubeus or Mimikatz.