Internet of Things Exploration: 2016 Ford Flex
David Fletcher// My wife and I recently purchased a 2016 Ford Flex to replace an aging version of the same make and model that met an untimely fate. During the […]

David Fletcher// My wife and I recently purchased a 2016 Ford Flex to replace an aging version of the same make and model that met an untimely fate. During the […]

David Fletcher// This blog post is going to illustrate setting up a software access point (AP) on Ubuntu 16.04. Having the ability to create a software AP can be very […]

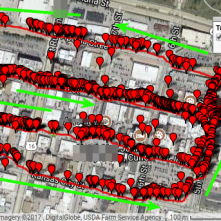
Mike Felch // Meet ‘The Box’ Bomb For the last few years at the security conference DEF CON in Las Vegas, the Tamper Resistant Village has hosted a challenging contest called […]

CJ Cox // We frequently get requests from customers asking us if we provide consultation defending their systems. The other day I got a question from a customer asking us […]
Jordan Drysdale // Step 1: Build your capture rig RPi3, Kali, Battery Packs, 2 x supported wifi card of your choosing (I used the Alfa Black for this run). My finished product: Solar Battery […]
John Strand // New to InfoSec? Mentoring someone new to the industry? Here’s John’s advice if he had to do it all over again. Sierra is on replying to your […]
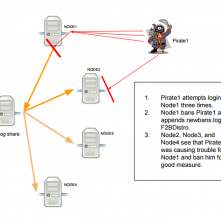
Kent Ickler // How to Configure Distributed Fail2Ban: Actionable Threat Feed Intelligence Fail2Ban is a system that monitors logs and triggers actions based on those logs. While actions can be […]
David Fletcher // During our testing, we encounter organizations of various different sizes, shapes, and composition. One that we’ve run across a number of times includes a fairly even mixture […]
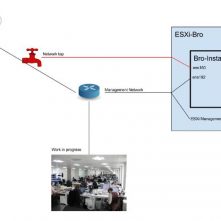
Kent Ickler // You’ve heard us before talk about Bro, an IDS for network monitoring and analysis. We’ve had several installs of Bro over time here at BHIS. It’s about […]