Bugging Microsoft Files: Part 2 – Xlsx Files using Microsoft Excel
Ethan Robish // As promised in my previous post, part 1, this post shows how to place a tracking bug in a native .xlsx file. Full credit for this method […]
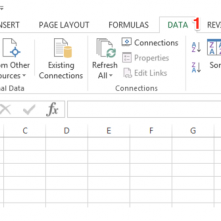
Ethan Robish // As promised in my previous post, part 1, this post shows how to place a tracking bug in a native .xlsx file. Full credit for this method […]

Dakota Nelson* // Part 4: Resilient Steganography This is it. The end. The last of a four part series covering image steganography. You can get started with part 1, part […]
Carrie Roberts // There are various reasons why having a webDAV server comes in handy. The main reason I created one was to execute a malicious Outlook rule attack as […]

Ethan Robish // If you’re familiar with ADHD and Web Word Bugs, you likely already know the method to create web tracking software using .html files renamed as .doc files. […]

Dakota Nelson * // This is part three of a four part series. In part 1, we covered the basics of image formats and found a place to hide data […]

Beau Bullock // Full Disclosure: Black Hills Information Security believes in responsible disclosure of vulnerabilities. This vulnerability was reported to Microsoft on September 28th, 2016. As of the publication date of […]
Melisa Wachs // Everyone seems to hates clowns these days. With all the crazy clown sightings, and banning of clown costumes at parades and schools, I got to thinking that […]

Brian King // News from Google this week says that Chrome will start enforcing Certificate Transparency a year from now. https://groups.google.com/a/chromium.org/forum/#!topic/ct-policy/78N3SMcqUGw This means that when Chrome contacts a website, if […]

David Fletcher & Sally Vandeven // We gave a presentation at the GrrCon hacker conference in Grand Rapids, MI on October 6, 2016. The presentation was a dialogue meant to illustrate the […]