Small and Medium Business Security Strategies: Part 1
Jordan Drysdale// Blurb: A few of us have discussed the stress that small and medium business proprietors and operators feel these days. We want to help stress you out even […]

Jordan Drysdale// Blurb: A few of us have discussed the stress that small and medium business proprietors and operators feel these days. We want to help stress you out even […]
John Strand // I wanted to take a few moments and address the “Hacking Back” law that is working people up. There is a tremendously well-founded fear that this law […]
Lidia Giuliano//* The endpoint protection space is a hot market. With statistics showing malware creation ranging from 300,000 to a million pieces a day, traditional signatures just can’t keep up. […]

Beau Bullock, Brian Fehrman, & Derek Banks // Pentesting organizations as your day-to-day job quickly reveals commonalities among environments. Although each test is a bit unique, there’s a typical path […]
Derek Banks // I want to expand on our previous blog post on consolidated endpoint event logging and use Windows Event Forwarding and live off the Microsoft land for shipping […]
Derek Banks, Beau Bullock, & Brian Fehrman // Our clients often ask how they could have detected and prevented the post-exploitation activities we used in their environment to gain elevated […]

This is the in-studio version of our live in DC event from July. In this webcast, John covers how to set up Active Directory Active Defense (ADAD) using tools in […]
Logan Lembke// Here at BHIS, we ♥ Bro IDS. Imagine… Bro IDS Everywhere! If you haven’t encountered Bro IDS before, checkout this webcast on John’s Youtube channel discussing the need for Bro […]
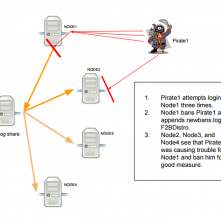
Kent Ickler // How to Configure Distributed Fail2Ban: Actionable Threat Feed Intelligence Fail2Ban is a system that monitors logs and triggers actions based on those logs. While actions can be […]