Cisco Smart Install Escalation and Update!
tl;dr
Both Cisco and Nessus have escalated the Smart Install Client Service feature/vulnerability.
Nessus is now reporting the Smart Install RCE as critical. High five!!!
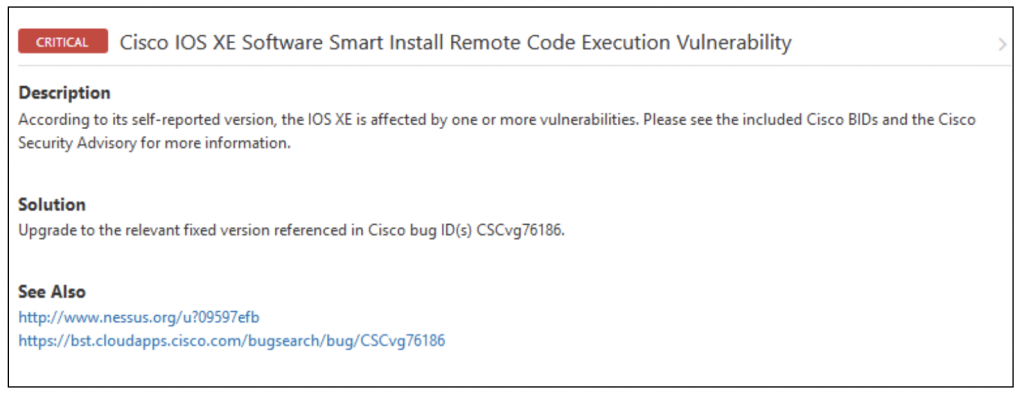
Cisco has also packaged up a couple of associated bugs, one of which requires a firmware update. The first is seen below:
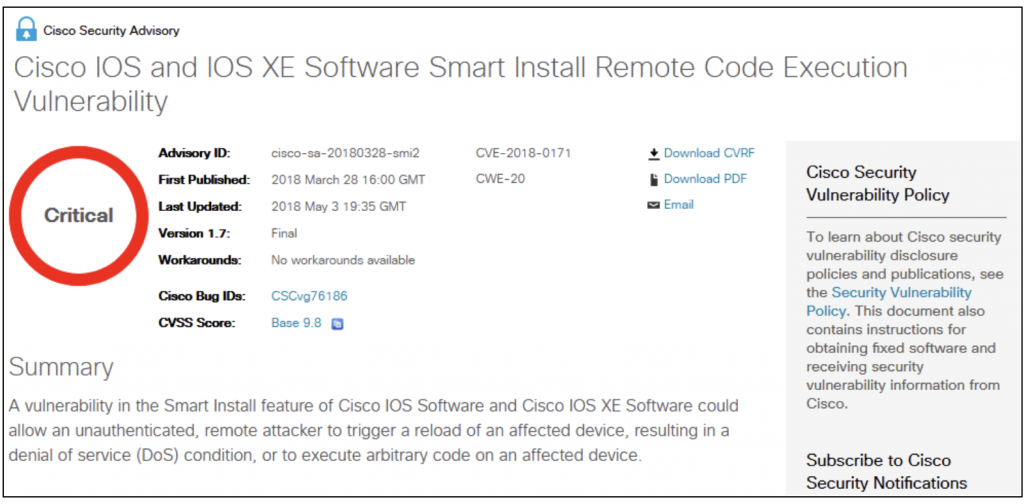
Reference to this advisory is listed here:
https://tools.cisco.com/security/center/content/CiscoSecurityAdvisory/cisco-sa-20180328-smi2
And, the latest update posted on 7-December-2018 lists the service as potentially dangerous and that the best practices configuration would not leave this service “lying around” for someone to stumble upon.
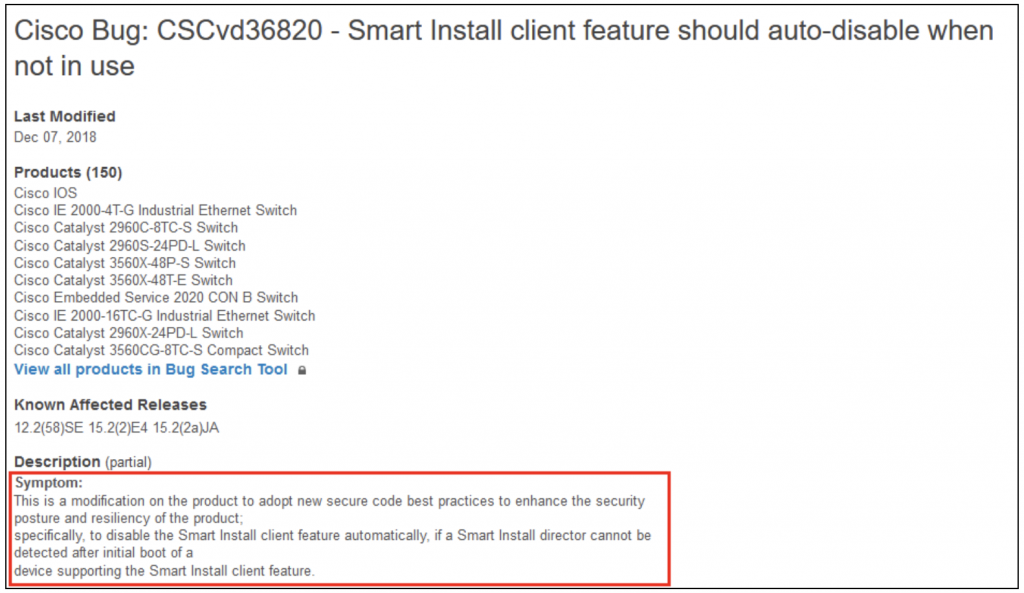
While the screenshot and text as seen above suck, the point is well received. The problem? It appears that based on the reference material, you will need a SmartNet or equivalent contract to get your hands on the updated software/firmware/IOS.
Reference:
https://quickview.cloudapps.cisco.com/quickview/bug/CSCvd36820
Good luck and happy patching!
Want to learn more mad skills from the person who wrote this blog?
Check out these classes from Jordan and Kent:
Assumed Compromise – A Methodology with Detections and Microsoft Sentinel
Available live/virtual and on-demand!

