Getting Started With ROT Obfuscation
Hello, my name is John Strand. In this video, we’re going to be talking about ROT or rotate. Why exactly are we talking about one specific thing? Well, this particular video is used with our Cyber Range that we’re establishing at Black Hills Information Security and it’s very common when you’re pentesting or you’re doing any type of cyber range activity or capture the flag to encounter a variety of different types of encoding and ROT is just one of them.
Specifically, we’re going to talk about ROT 13. You can also see ROT 47 but we’re going to be talking a little bit about ROT 13 to kick it off.
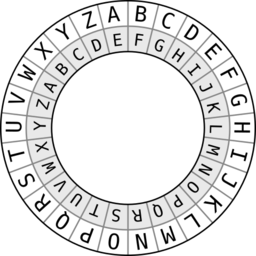
Now, whenever you’re looking at ROT, it means rotate. This is a variation of the Caesar Cipher where you could say R1 or rotate one, that means an A becomes a B, R2 would be an A becomes a C, and so on. So you’re basically rotating the characters. Now the way that this used to work with the Caesar Cipher is you’d wrap it around a pole and the rotation would actually line up on the pole itself. But we can actually do that with computers.
Now, why in the hell would anybody ever do this? Well, it actually became a very popular thing back in the ’80s on various Usenet groups, basically bullet boards. And what was going on was you would have jokes or you would have text and you would want to obscure the punchline. So somebody would read the setup for the joke and then the punchline would be like ROT encoded. Then you could basically decode it, get the punchline. And that would be funny.
It was also kind of the equivalent of magazines, like MAD magazine would have a quiz and then you would turn it upside down and you would see it. So that was kind of the way that they actually utilized it. So originally, it was set up as just a joke. And that works, I guess. But okay, so things were different back then, whenever it came to humor.
But whenever we’re looking at ROT and various variations of ROT, you’re actually still seeing it being used in some applications. Now, this is never a good idea, ever. Just don’t ever allow your developers to use things like ROT. But as a security professional, you got to be able to understand when you see it, how to be able to identify it quickly and then eradicate it like you would a termite or roach someplace.
So if we’re going to play around with ROT, we’re going to be using the TR translate command on Linux to actually do this. I’m going to just take a basic bit of text and I’m just going to echo it through. So I’m going to echo “I am sure there’s a better way to do this!!!!!!” and then we’re going to pipe it through TR. What you’re seeing with that TR command is we’re basically saying translate and shift. We have capital A to capital Z, lowercase A to lowercase Z, and then it’s going to translate that to an N. And that means N is going to be the starting character. So if you go A, B, C, D, E, F, G, H, I, J, K, L, M, N, that’s 13. So it’s going to rotate it over. So it’s basically going to turn this text that I have, “I am sure there’s a better way to do this!!!!!!” and we’re going to translate it. And whenever I hit enter, you can see that it’s converted it over to jibberish. If you play that backward, it brings your dogs and cats back to life.
So that’s a really easy way to try to shift that. Of course, you can reverse it to try to get it down into normal text that we would be able to read a little bit easier.
So the whole point of all of this is whenever you’re dealing with capture the flags or any of these different challenges that are online, you’re going to come up with ROT. It’s going to be something you’re going to run into. It’s kind of an inside joke from years back.
However, there have been situations where we have actually seen this used in an application to obfuscate things like passwords. Now, trust me, there’s far better ways to obfuscate passwords, but if you’re a developer fresh out of community college and you’ve got to do some security and you don’t understand security at all, this seems like a quick and easy way to try to obfuscate.
So some of the dead giveaways are the spacing and the lines themselves. If you have V, N, Z. So V, most of the English language is going to be multiple letters. So you would focus in on translating a V to like an I or a V to an A and so on, and then counting that offset and then doing that offset shift back to see if you can get it into something that’s more useful.
Now there’s other versions of ROT. If you start seeing special characters being used, you might be using something or encountering something like ROT 47 or ROT 40 or some other variation that can use higher value ASCII characters. That means that they’re actually rotating through the special characters as well. If you get that, you’ll just have to play around with the different types of ROT encodings to play with it, but usually most CTFs, they don’t go off the main ones that are normally used.
So I hope you like this video. Once again, this is being used with the BHIS Cyber Range. You’ll see other ones pop up for things like BASE64 encoding and using hex editors and things of that nature. So thank you so much and I hope to see you in a new video sometime soon.
Want to level up your skills and learn more straight from John himself?
You can check out his classes below!
Active Defense & Cyber Deception
Available live/virtual and on-demand

