If You Don’t Ruse, You Lose: A Simple Guide to Blending in While Breaking In
Are you assigned a physical penetration test and want to fly under the radar and meet all of your objectives like the elite hacker you are? Stick around and let’s go over a few things that might help you blend in or stay undetected.
What is a Ruse?
What is a ruse exactly? A ruse is a method used to outwit someone by deceiving them. A ruse may involve a deceptive plan, statement, or device used. The context we are using here is based on what you wear and how you appear.
OSINT
The best ruse might be the one you research. Look for these things:
- Local College or Pro Teams:
- What city or state is the assessment taking place? Get an idea of a subject that you could brush up on and talk about. Sports are a great icebreaker.
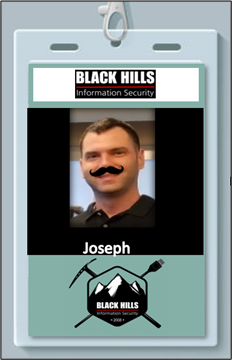
- Company ID Cards:
- Check a company’s social media. Figure out what ID cards look like and try to replicate one yourself using a Canon IVY or similar.
- Company Events:
- Through a company’s site or social media, try to find picnics, unveiling ceremonies, fundraisers, or even softball games. These are all events you could find badges to replicate, clone, or tailgate your way in among the madness for easy access.
- Construction work
- Construction sites for a company often do not have things in place such as network access control (NAC) or monitoring. If your goal is network access, this may be your golden ticket.
- Locations
- What locations did the customer give you to penetrate and what is your goal exactly? It is always helpful to research the locations you are assigned to and also other sites you may find. Try to identify what kind of access controls there are or dress code for those locations (datacenters may be more relaxed than corporate headquarters). If you have trouble meeting your objectives, have an idea of other locations that may help you reach your objectives if communicated with the customer.
Badges
If you have seen any badges posted publicly from your adventures in OSINT above, try to replicate it. Also, try to mimic the badge placement on-site for your physical penetration test. Even if you aren’t able to clone or get legitimate badge access, a well-made counterfeit badge might let you tailgate right behind an actual employee.
Pretext
Security conscious employees got you down? Pretext may help. What is pretext? In this context, it’s as simple as having a story about why you are somewhere or even why you need to be somewhere. If you are in a networking closet, have a story about router upgrades. If you are in someone’s office after hours, you are fulfilling some janitorial duties. Matching your pretext with your ruse is recommended.
Utility Worker
The utility worker ruse is a fairly common ruse among penetration testers who perform physical security engagements. It’s not unusual to have a few industrial maintenance employees around keeping the facility running the way it should. Unfortunately, this ruse is also being seen by criminals who burglarize and steal packages off porches.

Security Guard
Posing as a security guard is also a good ruse to work with. A few caveats: don’t act like a cop, you might have a bad time. Security guard ruses can work just fine; do some due diligence if you can. See if there are already security guards there. If there are, you might want to find an alternative ruse.

IT Worker
IT workers are never a bad idea. You can dress normally and have less eyes on you as opposed to a security guard or having people wonder what kind of work you are doing in your utility jacket and hard hat. An added bonus is that IT workers can slide right by with all your lockpicks, traveler hooks, tensioners, and drop boxes inside of a typical laptop case or backpack.

Pregnancy Ruse
Last but not least, a pregnancy ruse could also help you get into many places. People are often extra helpful in this situation. Although faux pregnancy bellies are not cheap, they are effective.

Hopefully this gives you a few simple ideas to use or expand upon during your next physical security assessment.
Check out another blog by Joseph about physical pentests: Tales From the Pick: Intro to Physical Security Tools
Ready to learn more?
Level up your skills with affordable classes from Antisyphon!
Available live/virtual and on-demand

