Tap Into Your Valuable DNS Data
Joff Thyer // The Domain Name System (DNS) is the single most important protocol on the Internet. The distributed architecture of DNS name servers and resolvers has resulted in a […]
Joff Thyer // The Domain Name System (DNS) is the single most important protocol on the Internet. The distributed architecture of DNS name servers and resolvers has resulted in a […]

Slides for this webcast can be found here: https://www.blackhillsinfosec.com/wp-content/uploads/2020/09/SLIDES_AttackTactics6ReturnofBlueTeam.pdf In this webcast we walk through the step-by-step defenses to stop the attackers in every step of the way we showed […]
Dakota Nelson // Dakota talks about the pentester pyramid of pain and the different types of tests available from an information security firm. See his slides here: https://blackhillsinformationsecurity.shootproof.com/gallery/7404264/ Extra links & […]
Podcast: Play in new window | Download
Subscribe: Apple Podcasts | Spotify | Amazon Music | RSS
Kent Ickler // TL;DR: This post describes the process of building an active system to automatically recon SPF violations. Disclaimer: There are parts of this build that might not be legal […]
Kent Ickler // Link-Local Multicast Name Resolution (LLMNR) This one is a biggie, and you’ve probably heard Jordan, John, me, and all the others say it many many times. LLMNR […]

Rick Wisser// Here at BHIS we are always on the lookout for new toys. Especially if we can use them during a pentest. As a pentester, we all have a […]

The Story Behind the Shirtand making the right choice I understand that a lot of you came up and you were picked on. […] You were the one that was […]
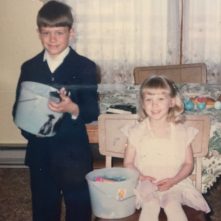
Melisa Wachs// Many of you have met John, so I thought you’d enjoy this posh little gem I dug up. This picture was taken in our first home, and although I […]

John Strand// In this webcast, John walks through a couple of cool things we’ve found useful in some recent network hunt teams. He also shares some of our techniques and […]