A Holiday Tale of Two Teams: The Blue Team Barbie & Red Team Elf on the Shelf saga
Staff // Thanks to everyone for all the good ideas! We had so much fun with this, and hopefully it made you laugh as much as we did. Happy December! […]

Staff // Thanks to everyone for all the good ideas! We had so much fun with this, and hopefully it made you laugh as much as we did. Happy December! […]

John Strand // Lately we’ve been running a very cool game with a few of our customers. There’s been some demand for incident response table top exercises. For the […]

Brian Fehrman // Privilege escalation is a common goal for threat actors after they have compromised a system. Having elevated permissions can allow for tasks such as: extracting local password-hashes, […]

Beau Bullock & Michael Felch // Source: https://chrome.google.com/webstore/detail/google-calendar-by-google/gmbgaklkmjakoegficnlkhebmhkjfich Overview Google Calendar is one of the many features provided to those who sign up for a Google account along with other popular […]
Derek Banks, Beau Bullock, & Brian Fehrman // Our clients often ask how they could have detected and prevented the post-exploitation activities we used in their environment to gain elevated […]
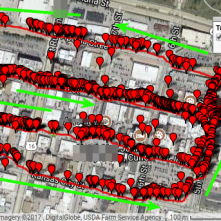
Jordan Drysdale // Step 1: Build your capture rig RPi3, Kali, Battery Packs, 2 x supported wifi card of your choosing (I used the Alfa Black for this run). My finished product: Solar Battery […]

Lee Kagan* // Deploying an offensive infrastructure for red teams and penetration tests can be repetitive and complicated. One of my roles on our team is to build-out and maintain […]
Joff Thyer & Derek Banks // Editor’s Note: This is a more in-depth write-up based on the webcast which can be watched here. As penetration testers, we often find ourselves […]

Kent Ickler // What is Cacti? Cacti is a network system that inputs system-generated quantifiable data and presents the data in spiffy graphs. Net-Admin In the Net-Admin world, it gives […]