Small and Medium Business Security Strategies: Part 2

A few of us have discussed the stress that small and medium business proprietors and operators feel these days. We want to help stress you out even more. Not really, but if you aren’t worrying about IT security, you are probably doing it wrong. This series will run through some of the important controls that IT pros have mapped out for us. We are trying to present these in a way that you can accomplish them without dedicated IT staff.
To start from the beginning of this series: Part 1 – Introduction to SMB InfoSec Controls
Part 2: Inventory
The first piece of the puzzle is sitting down and understanding at a minimal or conceptual level what it takes to keep your organization’s IT infrastructure operational. Do you have a modem and a phone line? Who do you call if service drops? Finding answers to these questions should help you sleep a little better at night. That said, there are a lot more of these questions specific to inventory controls.
Do you have an off the shelf device from an outlet store connected to your modem? Do you know the password or who configured it? Do you know what a router is? As the proprietor of any business, it is your job to delegate ownership of network inventory to someone you trust if you are not doing it yourself.
Taking Inventory
Spreadsheet Framework for Inventory Management:
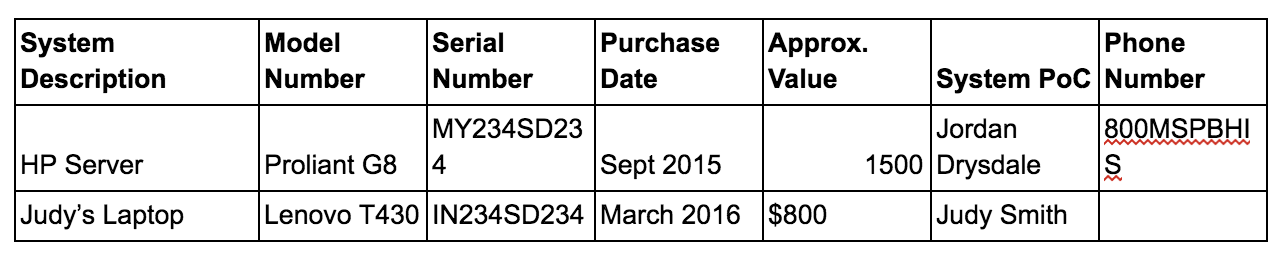
There should be a separate spreadsheet for servers, laptops, and workstations similar to the following:
Now it’s time to call a staff meeting. The purpose of this meeting is to help people understand that throughout the calendar year of 2018, the company will be transitioning and everyone is going to play a role. Ask your staff if they have had their identity stolen. Ask them if they are worried about hacking. Some of your employees will answer yes to the first and most to the second.
Delegation
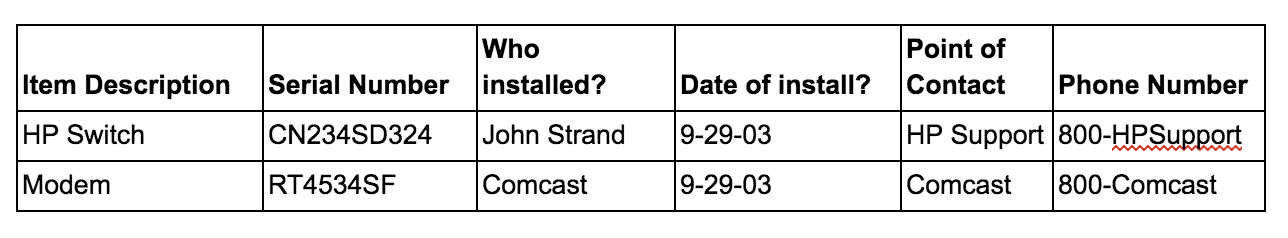
Let’s delegate some tasks. First, find the person with the most knowledge about systems and computers. This person gets to take a crack at the telecommunications area. They need to document the modem, any switches, routers, firewalls, wireless devices, et cetera. Next, each member of your team will need to provide the details of their system to the spreadsheet owner.
Network Configuration
There are at least a million unique ways to install and configure a small network. There is a very good chance your network may exist outside even these unique configurations. As a previous member of a ‘managed services’ team, it is very possible that you paid someone else to install, configure, and troubleshoot your network. It is also very possible that these folks are still in charge of your network.
Here’s a very strong case for managed services:
- Networks are complex and hard to manage.
- Without dedicated IT staff, it can be a nightmare to manage yourself.
- For a thousand bucks or so a month, having a dedicated team to answer trouble calls and show up when things are broken, this absolutely crushes the ROI of an FTE.
- Assuming you have a dedicated IT FTE, for even mildly complex networks, it is nearly impossible to know everything.
- Last, it so much easier to let someone else worry about these things.
Let’s look at the last bullet here: “Let someone else worry about your network.” This in itself is a dream and should be far from reality. Contact your managed services provider now and ask for an inventory of your networking gear. Follow up with a second request for the inventory spreadsheet of your servers, workstations, and laptops. If they don’t provide this in a timely fashion, it likely means they don’t have it. This demonstrates a flaw in their management of your network.
So, with a couple of spreadsheets and a plan, you too can maintain an accurate inventory of your network hardware. Your staff can help ease the burden and should feel empowered to do so.
The goal is not to run your business like Amazon runs its warehouses, but maybe someday?

Next up in series, we’ll cover some of the software inventory strategies that can help you finish out the inventory controls from the CSC.
Want to learn more mad skills from the person who wrote this blog?
Check out these classes from Jordan and Kent:
Assumed Compromise – A Methodology with Detections and Microsoft Sentinel
Available live/virtual and on-demand!

