Hide Payload in MS Office Document Properties
Carrie Roberts* // Can you think of a reason why you might want to put a lengthy comment into the properties of an MS Office document? If you can, then […]
John Strand// In this webcast John talks about the new ACDC law and what it means exactly. There has been quite a bit of anger and great GIFs about hacking […]
Sierra Ward with help from all // Wow, another year, another Christmas and another chance to be totally stumped by what to get you favorite InfoSecker. But fear not! We are […]
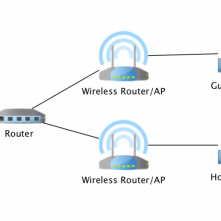
Ethan Robish // In this series of posts, I’ll discuss how I segmented my home network using VLANs and how I moved away from using a risky consumer-grade router at […]
John Strand // I wanted to take a few moments and address the “Hacking Back” law that is working people up. There is a tremendously well-founded fear that this law […]

Matthew Toussain // PowerShell is dead… well dying, kind of. JavaScript interpreters, on the other hand, are everywhere, and they are far from confined to the web browser. Join Matt […]

Gail Menius// The sky is clear, the air is so cool and crisp with the small dusting of snow muting the sounds of Deadwood you can almost hear the stars […]

Beau Bullock & Michael Felch // Source: https://chrome.google.com/webstore/detail/google-calendar-by-google/gmbgaklkmjakoegficnlkhebmhkjfich Overview Google Calendar is one of the many features provided to those who sign up for a Google account along with other popular […]
Lidia Giuliano//* The endpoint protection space is a hot market. With statistics showing malware creation ranging from 300,000 to a million pieces a day, traditional signatures just can’t keep up. […]