GNU Screen Quick Reference
Brian King // I use GNU Screen mainly to prevent processes from dying when I disconnect from an SSH session, but GNU Screen can do a whole lot more than that […]
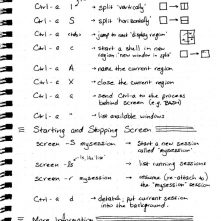
Brian King // I use GNU Screen mainly to prevent processes from dying when I disconnect from an SSH session, but GNU Screen can do a whole lot more than that […]
Carrie Roberts // Getting a shell using a malicious Outlook rule is an awesome tool during a pentest and great fun! Nick Landers had a great post including enough information to make […]

Dakota Nelson* // Part 4: Resilient Steganography This is it. The end. The last of a four part series covering image steganography. You can get started with part 1, part […]

Dakota Nelson * // This is part three of a four part series. In part 1, we covered the basics of image formats and found a place to hide data […]

BBKing // So I’m working the other day, and my wife asks me why the TV is on. I don’t know. I didn’t turn it on. But it’s near my […]

Dakota Nelson* // Part 1: Image Formats What if I told you this adorable puppy was hiding a secret message? In this post, we’ll find out how this dog was […]
Jordan Drysdale // This article, like the IADGov link here has three major steps. First, acquire a Raspberry Pi and a VPS running CentOS 6.8. Second, configure the server and Raspberry […]
Ethan Robish // Let’s Encrypt is a free service that allows you to obtain a free (as in beer) SSL/TLS domain validation certificate to use as you wish. Here is what […]