How to Identify Network Vulnerabilities with NetworkRecon.ps1
David Fletcher // Whenever I have the opportunity, I like to perform packet collection on a test for about five minutes so I can analyze the results and look […]
David Fletcher // Whenever I have the opportunity, I like to perform packet collection on a test for about five minutes so I can analyze the results and look […]

Sally Vandeven // OR How to Pentest with AD Explorer! Mark Russinovich’s Sysinternals tools (Microsoft) are nothing new. They have been a favorite among system administrators for many, many years. […]

Derek Banks // This post will walk through a technique to remotely run a Kerberoast attack over an established Meterpreter session to an Internet-based Ubuntu 16.04 C2 server and crack […]
Beau Bullock // Overview Microsoft Exchange users have the power to grant other users various levels of access to their mailbox folders. For example, a user can grant other users […]
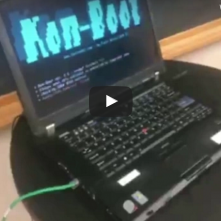
Jordan Drysdale, victim // Kent Ickler, adversary // In this post, our victim locks their computer and heads out for a coffee refill. The adversary smashes through all system and […]

Beau Bullock // Overview HostRecon is a tool I wrote in PowerShell to assist with quickly enumerating a number of items that I would typically check after gaining access to […]

David Fletcher // The following techniques serve to illustrate methods for obtaining C2 communication in a particular Cylance protected environment. The configuration of the centralized infrastructure and the endpoint agents […]

Sally Vandeven // All of the BHIS testers are pretty geeked about Hak5’s newest toy — the Bash Bunny. Last week, Jordan blogged about the USB Exfiltration payload. Today I […]

Carrie Roberts // A fun story from an adventure in social engineering not too long ago. Thought I’d pass on some things I learned and ways to be more prepared in the […]